Made for this Moment. Built for What’s Next.
Control where you need it and fully managed where you want it. Scale on your terms with a source-available framework you can host anywhere, or offload the operational heavy lifting to us with our fully managed B2B solution.
The Broadleaf Advantage
Broadleaf is built on true MACH principles — Microservices, API-first, Cloud-native, and Headless. Deploy on AWS, Azure, GCP, or on-premise, or let us manage it entirely through Broadleaf Cloud. Fully composable and cloud agnostic, every integration is on your terms, and your commerce architecture never outgrows the platform.
The Broadleaf Difference
-
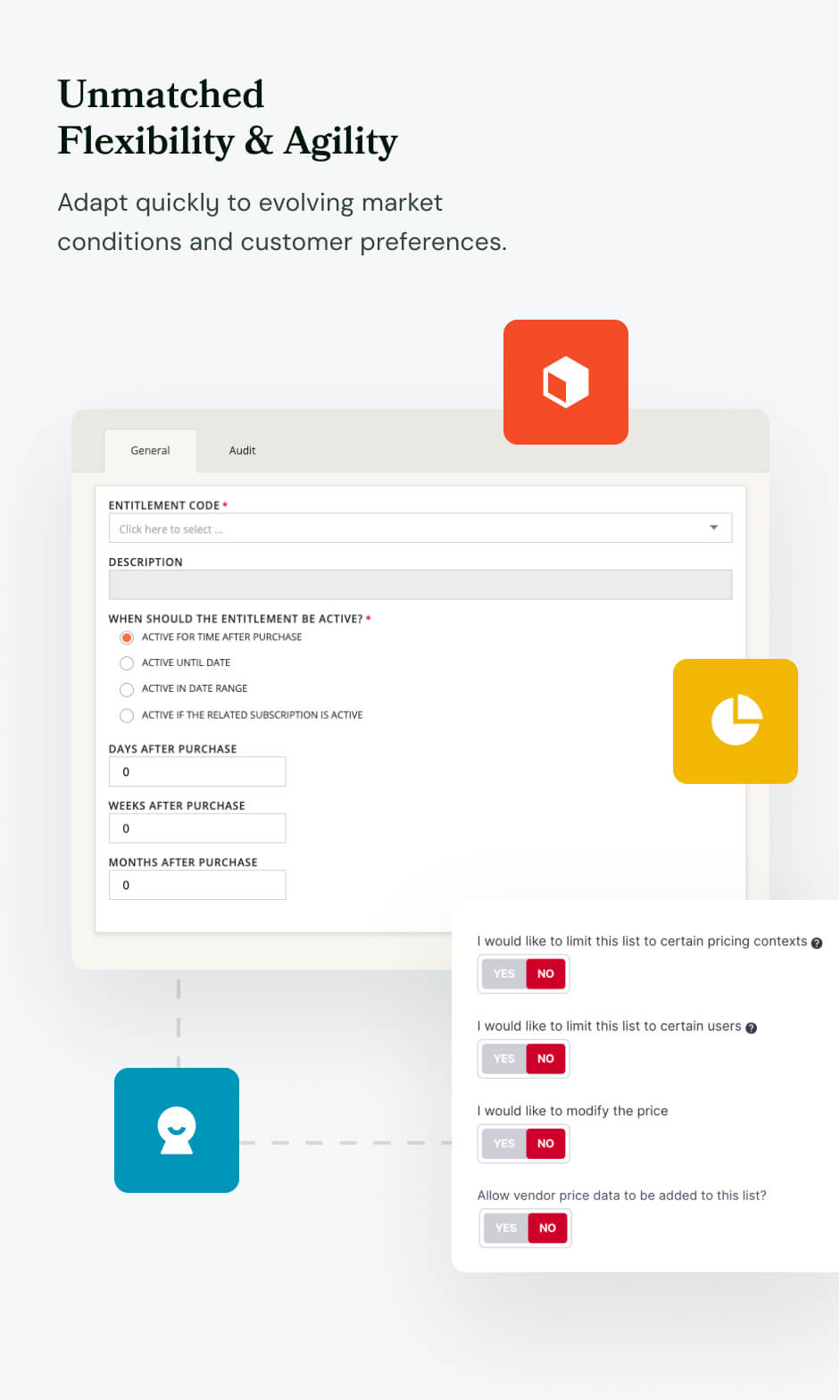
Built for
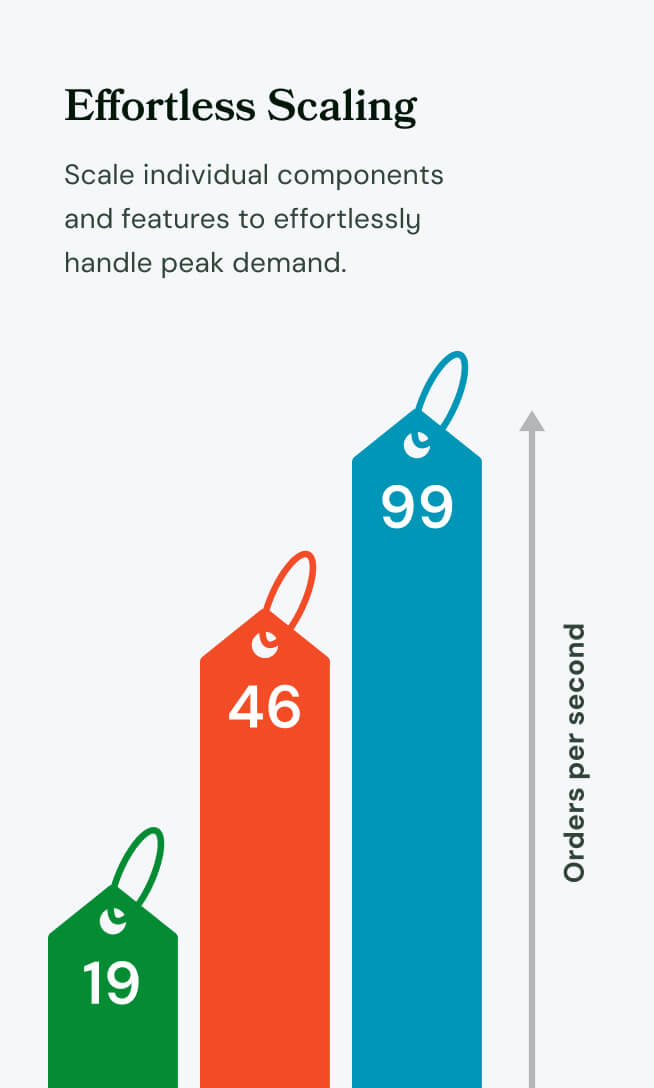
the Long HaulTrue microservices architecture means you replace, extend, or scale individual components without touching the rest of the platform. No forced re-platforming. No big bang upgrades.
-
Flexibility is
Our FoundationDeploy on-premise, in your cloud environment, in a hybrid configuration, or fully managed through Broadleaf Cloud. Integrate what you need, replace what you don't, and run your commerce infrastructure exactly where and how your business demands. Built around your business, not ours.
-
Composable MACH Architecture
Every component is independently deployable and interchangeable by design, not bolted on as an afterthought. Build a truly composable commerce foundation without vendor lock-in or architectural compromises.
-
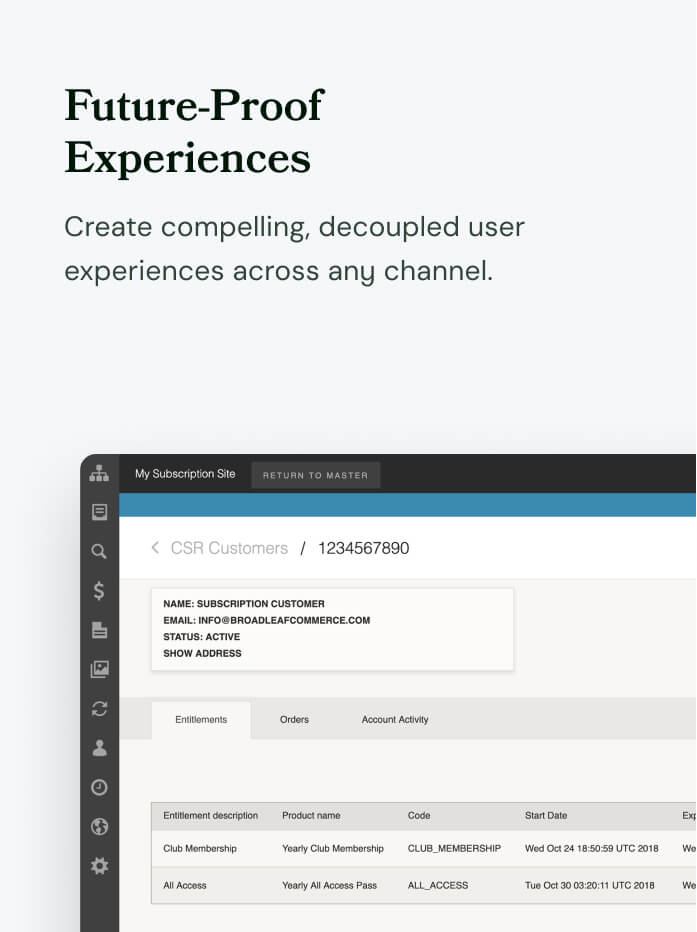
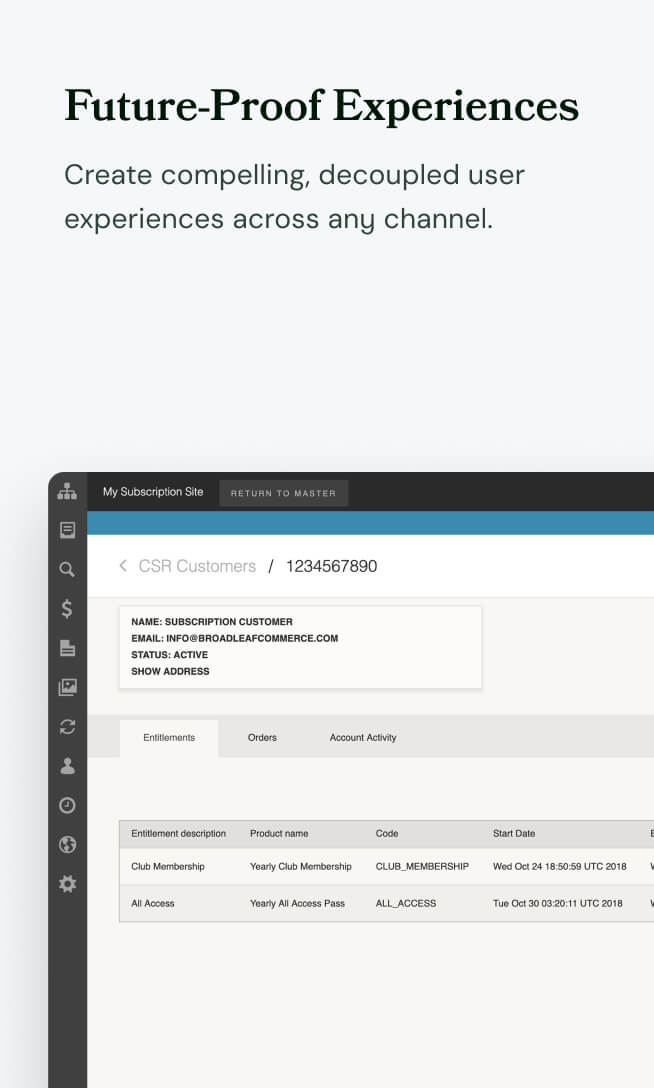
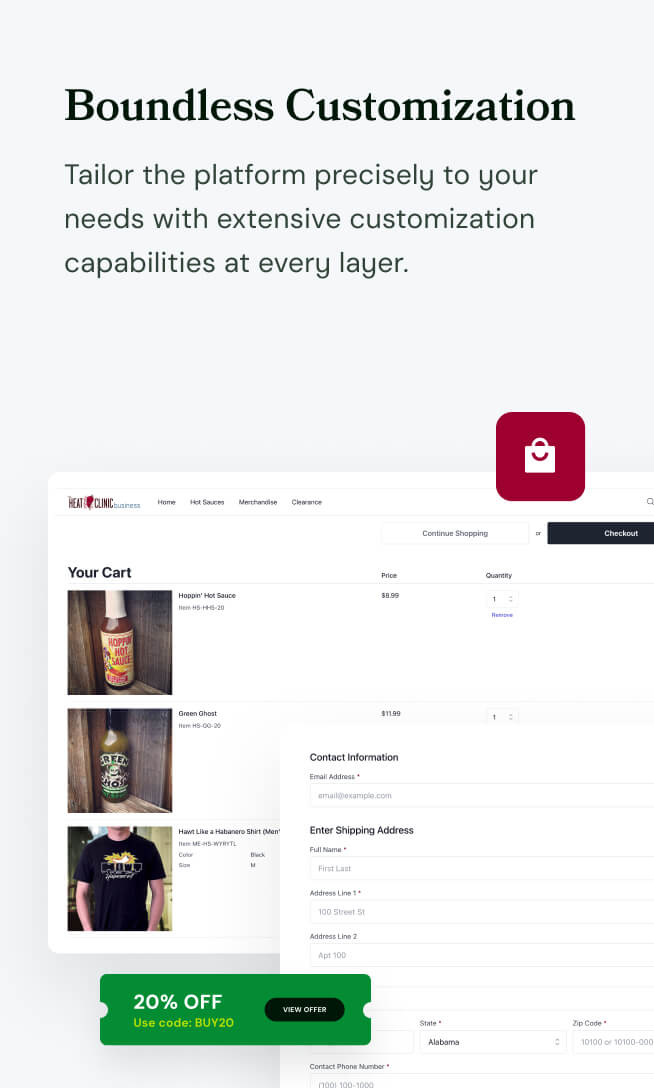
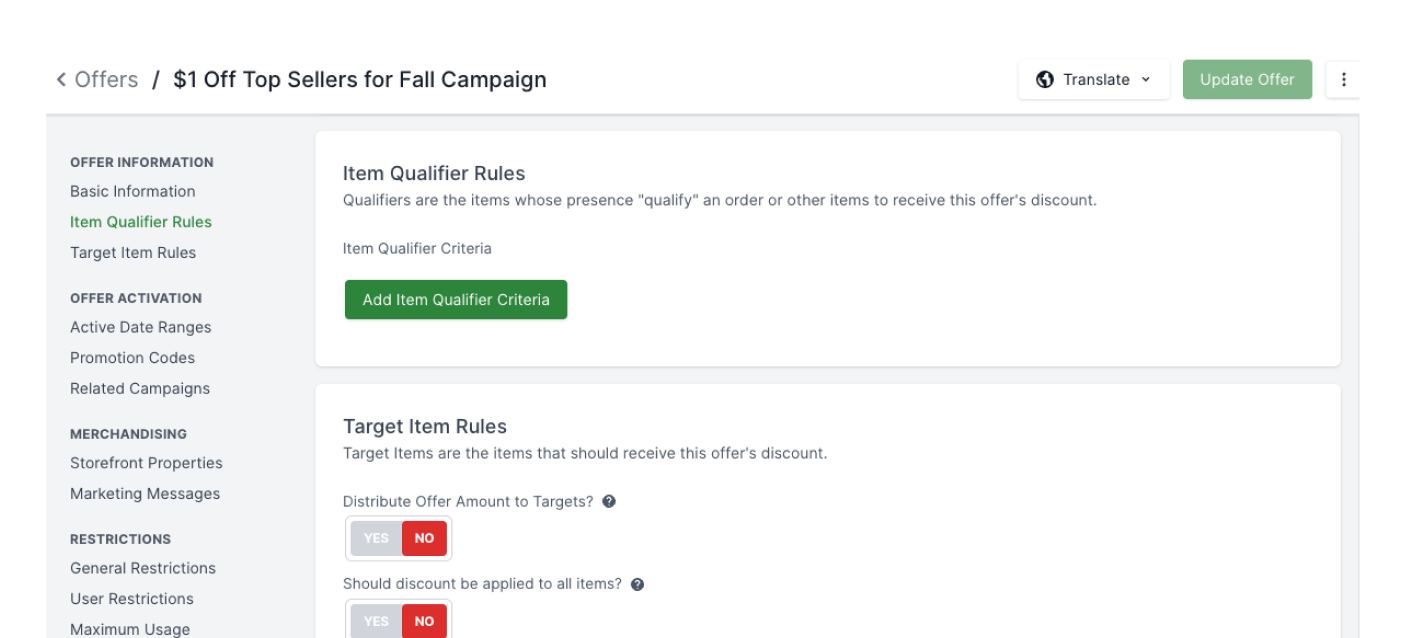
Extensible at Every Layer
Source-available software gives your team full access at every layer — APIs, data models, core application logic, and the Admin console. Customize everything, integrate anything, and build commerce experiences that are genuinely yours with no artificial ceilings on what's possible.
The MACH Advantage
for Open Commerce
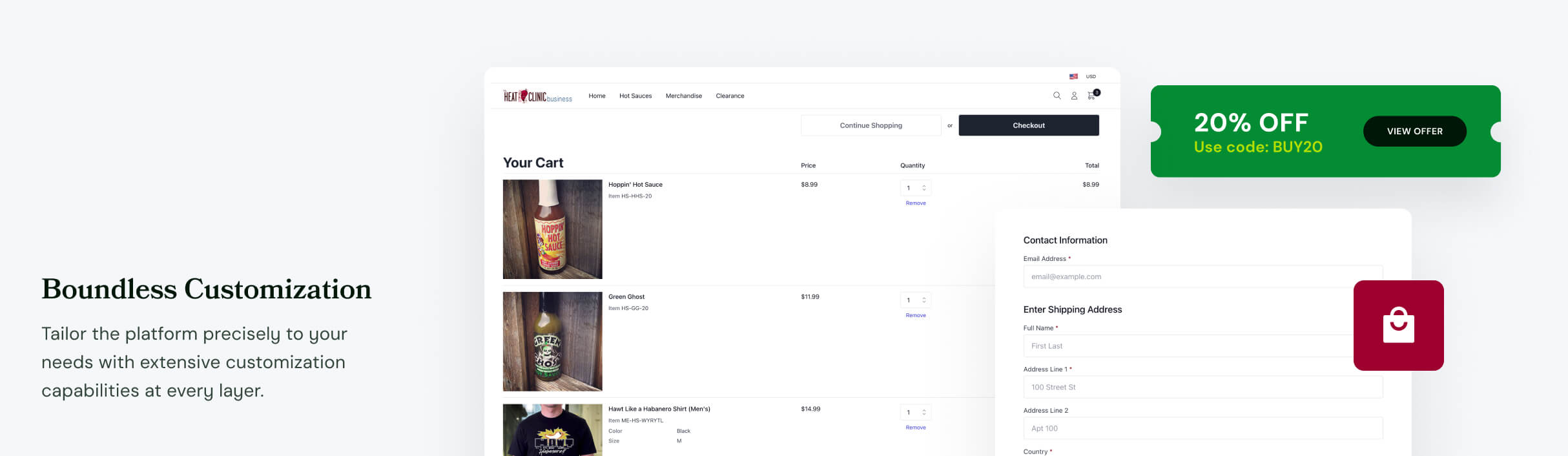
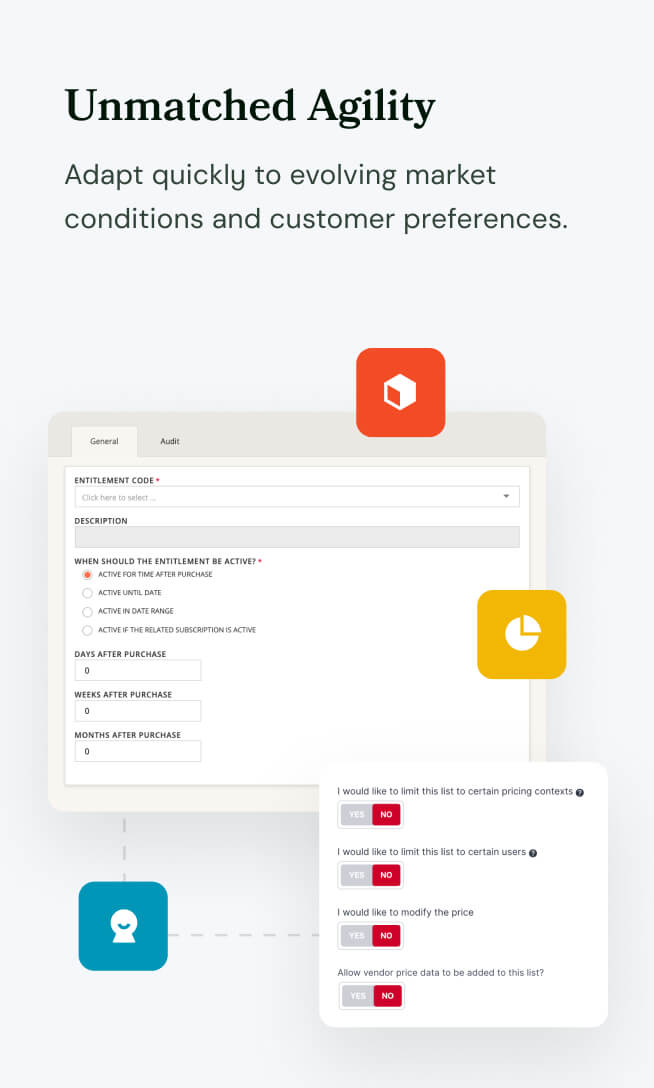
The Broadleaf microservices framework was built from the ground up with customization as a first-class concern. From the application to the APIs and even the Admin console, Broadleaf’s extension patterns make it uniquely yours.
Learn More